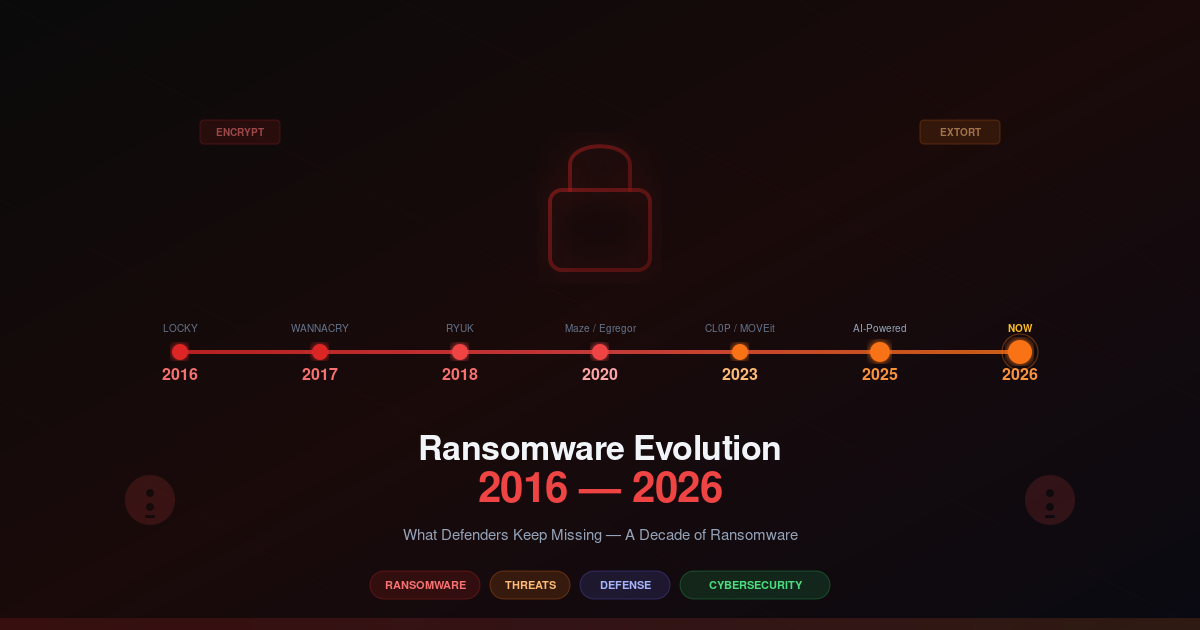
A Decade of Ransomware: 2016 to 2026
Ransomware Evolution: What Defenders Keep Missing
Ransomware Evolution: The Hidden Threats Defenders Miss
Ransomware didn’t appear overnight, but the last decade transformed it from a nuisance into an existential threat to critical infrastructure, healthcare, and supply chains. Understanding that evolution is the first step toward not becoming the next headline.
The Timeline
2016 — Locky: Distributed primarily through malicious macro-enabled Word documents in phishing emails, Locky encrypted files and changed extensions to .locky. It was the first ransomware family to generate tens of millions in ransom payments and set the template for email-based distribution that persists today.
2017 — WannaCry and NotPetya: WannaCry exploited the EternalBlue vulnerability (MS17-010) in Windows SMB, spreading to 230,000 systems across 150 countries in a single day. NotPetya, disguised as ransomware, was actually a wiper that caused $10 billion in damage — the most destructive cyberattack in history at the time. Both used NSA-leaked exploits.
2019 — Ryuk: Targeted ransomware that focused on large organizations. Attackers would dwell in networks for weeks or months before deploying Ryuk, maximizing the damage and ensuring backups were destroyed first. Average ransom demands hit $1-2 million.
2021 — Colonial Pipeline (DarkSide): The attack that forced the largest fuel pipeline in the US to shut down for six days, causing fuel shortages across the East Coast. DarkSide operated as RaaS and collected a $4.4 million ransom (later partially recovered by the FBI).
2023 — MOVEit Transfer (Cl0p): Instead of encrypting systems, Cl0p exploited a zero-day in the MOVEit file transfer software and stole data from thousands of organizations. The BBC, Shell, US government agencies, and hundreds of others were affected. This marked the full shift to data-theft extortion.
2024-2025 — Lock-and-Lease and Intermittent Encryption: Attackers no longer encrypt everything at once. They encrypt a small percentage of files each day, keeping the victim’s systems barely functional while maintaining constant pressure to pay. Some groups “lease” access back to victims — pay a weekly fee or we encrypt more.
From Encryption to Extortion
The business model shifted because encryption stopped working as well. Victims got better at restoring from backups, and law enforcement started recovering keys. The attackers adapted: if you can’t force payment through encryption, force it through the threat of publication.
Double extortion means encrypting data AND threatening to leak it. Triple extortion adds DDoS attacks against the victim’s public-facing services and direct outreach to the victim’s customers and partners with the stolen data. The Cl0p group runs a dedicated leak site on the dark web where they publish data from non-paying victims on a countdown timer.
Ransomware-as-a-Service (RaaS)
The ransomware ecosystem now mirrors legitimate SaaS businesses. The core group develops the ransomware, maintains the infrastructure, and provides support. Affiliates — independent criminal operators — pay for access, conduct the actual intrusions, and split the ransom (typically 70-80% to the affiliate, 20-30% to the RaaS operator).
Initial Access Brokers (IABs) sell network access to affiliates. A VPN credential might sell for $500, RDP access for $1,000, and access to a Fortune 500 network for $5,000+. This marketplace lowers the barrier to entry — affiliates don’t need to be skilled at initial access, just at encryption and negotiation.
Common Attack Vectors in 2025-2026
- Phishing: Still the top vector. Malicious attachments, QR code phishing (quishing), and credential harvesting pages remain effective.
- VPN exploits: Fortinet, Pulse Secure, and Cisco VPN appliances continue to be exploited. Many organizations run unpatched VPN firmware because the update process requires downtime.
- Unpatched edge devices: File transfer appliances (MOVEit), firewalls, and remote management Tools are prime targets.
- Valid accounts: Attackers buy credentials from IABs and log in with legitimate accounts, bypassing MFA through token theft or session hijacking.
What Defenders Keep Getting Wrong
Incident response plans that exist only on paper. Most organizations have a plan. Few have tested it with realistic tabletop exercises. When the actual incident happens, the plan falls apart because nobody remembers who does what, communication channels are unclear, and decision-making authority is ambiguous.
The backup problem. Organizations backup their data but don’t test restoration. When they need to restore, they discover the backups are incomplete, corrupted, or — worst of all — also encrypted by the ransomware because the backup server was on the same network segment.
No network segmentation. A single compromised workstation should not give an attacker access to domain controllers and backup servers. Yet in most breach investigations, lateral movement is trivial because flat networks are still the default.
Slow detection. The average dwell time before ransomware deployment is still measured in weeks. Organizations lack the visibility to detect the reconnaissance, credential harvesting, and lateral movement that precedes the encryption event.
Modern Defense Strategies
- Immutable backups: Backups that cannot be modified or deleted, even by an administrator. Use object locking (S3 Object Lock, Azure Immutable Blob Storage) or air-gapped backup media. Test restoration monthly.
- Zero Trust architecture: Verify every access request regardless of network location. Implement micro-segmentation so a compromised endpoint can’t reach critical systems.
- EDR/XDR: Endpoint detection and response tools catch ransomware behaviors — mass file encryption, shadow copy deletion, registry modifications — before they complete. XDR extends this visibility across network, email, and cloud.
- Deception technology: Deploy fake credentials, fake file shares, and fake services. When attackers interact with them, you get an early warning before they reach real assets.
- Ransomware negotiation playbooks: Know in advance whether you’ll pay, who has authority to negotiate, and what your communication strategy is. Engage incident response retainers before you need them.
If you’re building a ransomware response plan, check out our CISO Guide to Ransomware Response Checklist.
The Economics of Ransomware
The ransomware ecosystem isn’t just a criminal nuisance — it’s a mature industry with estimated annual revenues of $1–2 billion, placing it on par with mid-sized SaaS companies. Chainalysis and FBI estimates suggest that known ransomware payments alone exceeded $1.1 billion in 2023, and the actual figure is likely higher given unreported incidents and settlements negotiated through intermediaries.
The economics are brutally simple. A single successful attack on a mid-market enterprise can yield $500,000 to $5 million. Multiply that across dozens of victims per operation, and a well-run ransomware group can clear tens of millions annually. Compare that to the cost of defending: enterprise cybersecurity budgets average $5–15 million per year, and even then, most organizations still get hit.
The true cost to victims extends far beyond the ransom itself. Downtime costs typically run 10 to 50 times higher than the ransom demand. A hospital losing access to patient records for two weeks doesn’t just pay a ransom — it loses revenue from cancelled procedures, faces regulatory fines, absorbs litigation costs, and suffers reputational damage that can take years to repair. The Change Healthcare breach in 2024 demonstrated this on a massive scale, with estimated total costs exceeding $8.7 billion.
The insurance industry has become a critical enabler of this ecosystem, whether intentionally or not. Cyber insurance premiums have surged, but insurers continue to pay ransoms when the math makes sense. Some policies explicitly cover ransom payments, creating a perverse incentive structure. Meanwhile, insurers are tightening requirements — mandating MFA, endpoint detection, and incident response plans — but the fundamental business model remains: pay out or go bankrupt defending.
Where does the money go? Ransomware groups operate like tech startups with dark budgets. A significant portion goes to infrastructure — bulletproof hosting, exploit development, and maintaining access brokers. Another chunk funds initial access brokers who sell network access for $500 to $10,000 per entry point. Some groups invest in zero-day vulnerabilities, paying six-figure bounties for unpatched exploits. And increasingly, funds flow toward insider recruitment, bribing employees or contractors to install backdoors or disable security controls.
Ransomware Groups to Watch in 2026
The ransomware landscape in 2026 is defined by a handful of persistent, adaptable operations. Here are the groups defenders should have on their radar:
LockBit
The most resilient ransomware operation in history. Despite a coordinated law enforcement takedown (Operation Cronos) in early 2024 that seized infrastructure and arrested key affiliates, LockBit returned within months with an updated locker and a renewed affiliate program. Their strength lies in operational simplicity and a massive affiliate network. LockBit doesn’t innovate technically — they iterate on a proven model with aggressive recruitment and high affiliate payouts (up to 90% of ransom to affiliates). They target everything from SMEs to Fortune 500 companies and remain the most prolific group by volume of attacks.
BlackSuit / Royal
Originally operating as Royal before rebranding to BlackSuit, this group has been linked to attacks on over 350 organizations. They favor double extortion and have been known to contact victims’ customers and partners directly to pressure payment. BlackSuit’s code shares overlaps with the now-defunct Conti operation, suggesting lineage from one of the most successful ransomware families in history. They tend to target professional services, manufacturing, and healthcare sectors.
Akira
Akira has carved out a niche targeting small and medium-sized businesses, particularly those running Cisco VPNs without MFA — a remarkably specific and effective entry vector. Their ransom demands are calibrated to what SMBs can actually pay, typically $200,000 to $1 million. This lower price point means higher payment rates. Akira has also shown interest in Linux systems, deploying variants that target VMware ESXi environments, which allows them to encrypt an organization’s entire virtual infrastructure in minutes.
RansomHub
RansomHub emerged in early 2024 and rapidly became one of the most dangerous operations in the space, with a particular focus on healthcare and critical infrastructure. Their attack on Change Healthcare in February 2024 disrupted prescription processing across the United States for weeks. RansomHub operates a strict affiliate vetting process, which paradoxically improves their success rate — fewer attacks, but higher quality operations. They’ve publicly criticized other groups for being “too greedy” and claim to negotiate more reasonably, though this is likely a psychological tactic rather than genuine goodwill.
Scattered Spider
Also known as UNC3944, Scattered Spider represents a different model entirely. Rather than relying on automated exploitation, they specialize in social engineering — impersonating IT staff in phone calls, conducting SIM swaps, and using elaborate pretexting to bypass MFA through social manipulation rather than technical defeat. Their operators are younger (many in their late teens and early twenties) and highly adaptable. They’ve been linked to attacks on MGM Resorts, Caesars Entertainment, and multiple cloud service providers. Their success demonstrates that no amount of technical security controls can fully compensate for human vulnerability.
The Role of Cryptocurrency
Ransomware and cryptocurrency are inseparable. Bitcoin remains the dominant payment method, but the mechanics of how ransom funds move have become increasingly sophisticated.
When a victim pays, the Bitcoin doesn’t go directly to an attacker’s wallet. Instead, it enters a laundering pipeline that can involve multiple stages: initial collection wallets, transfer through mixers and tumblers (services that pool and redistribute cryptocurrency to obscure origins), conversion through decentralized exchanges (DEXs) that require no KYC, and finally extraction to fiat currency through offshore exchanges or peer-to-peer arrangements.
The effectiveness of blockchain tracing has diminished significantly. While early ransomware operations (2016–2019) sometimes moved funds carelessly, modern groups employ techniques like chain hopping (converting between cryptocurrencies), peel chains (gradually splitting transactions), and nested services (using legitimate exchange services to mask illicit flows). Chainalysis and similar tools can trace movements, but attribution remains difficult, and funds frequently end up in jurisdictions with no extradition treaties or cooperative legal frameworks.
The shift toward Monero and other privacy coins is accelerating. Monero’s privacy features — ring signatures, stealth addresses, and confidential transactions — make it effectively untraceable by default. Several groups now demand payment exclusively in Monero, and others offer discounts for privacy coin payments. This trend directly undermines one of law enforcement’s primary investigative tools.
The Regulatory and Legal Landscape
Government responses to ransomware have shifted from reactive to proactive, and the regulatory environment is tightening rapidly.
In the United States, the SEC’s cyber incident reporting rules (effective December 2023) require public companies to disclose material cybersecurity incidents within four business days. This has fundamentally changed how organizations handle ransomware — the calculus now includes the market impact of disclosure alongside operational recovery. The Cyber Incident Reporting for Critical Infrastructure Act (CIRCIA), proposed in 2022 and moving toward implementation, will require critical infrastructure operators to report significant cyber incidents within 72 hours and ransom payments within 24 hours.
The EU NIS2 directive, which took effect in October 2024, significantly expands the scope of regulated entities and introduces stricter security requirements across all member states. Organizations in healthcare, energy, transport, and digital infrastructure must now implement risk management frameworks, report incidents within 24 hours of awareness, and face penalties of up to €10 million or 2% of global annual turnover for non-compliance.
The most contentious debate in this space is whether to ban ransom payments entirely. Proponents argue that a ban would destroy the business model by eliminating the revenue stream. Critics counter that it would simply punish victims — forcing them to choose between bankruptcy and legal consequences. Some countries, including France and parts of Australia, have moved toward restrictions or at least mandatory reporting of payments. The reality is nuanced: a payment ban without adequate support for victims would be catastrophic, but the current model of quiet payments with no consequences perpetuates the cycle.
Ransomware in Critical Infrastructure
The convergence of IT and OT (operational technology) environments has created an expanding attack surface that most organizations are fundamentally unprepared to defend.
The Change Healthcare breach in February 2024 remains the most impactful critical infrastructure attack in recent memory. A single point of failure — Change’s claims processing platform — cascaded across the entire US healthcare system. Pharmacies couldn’t process prescriptions. Hospitals couldn’t verify insurance. Patients couldn’t get medications. The disruption lasted weeks and affected an estimated one-third of all Americans. The attackers exploited a lack of MFA on a Citrix remote access gateway — a vulnerability that had been documented for years.
Energy and water systems face similar risks. OT/ICS environments were designed for availability and safety, not security. Many run legacy systems — Windows 7, Windows XP, or even older — that can’t be patched without breaking critical processes. Network segmentation between IT and OT is often incomplete or non-existent. When ransomware crosses that boundary, the consequences aren’t just data loss — they can be physical damage, environmental release, or loss of essential services.
Municipal governments remain disproportionately vulnerable. With limited budgets, aging infrastructure, and small IT teams, cities and towns are attractive targets precisely because they can’t afford to be down. Attacks on municipal water treatment facilities, emergency dispatch systems, and public transportation networks have demonstrated that ransomware in critical infrastructure isn’t a theoretical risk — it’s a recurring reality.
The path forward for critical infrastructure defense requires acknowledging an uncomfortable truth: air-gapping OT networks, implementing zero-trust architectures, and building incident response capabilities that account for physical consequences aren’t optional investments. They’re existential necessities.
Conclusion
Ransomware in 2026 is more sophisticated, more targeted, and more persistent than at any point in the last decade. The shift to extortion means backups alone aren’t enough. Defense requires layered controls: prevent initial access, limit lateral movement, detect early, and have tested response procedures. The organizations that survive ransomware attacks are the ones that practiced for them before they happened.
Reference: CISA Ransomware Guide
Reference: Europol IOCTA Report