Zero Trust Architecture for AI Systems: Implementation Guide
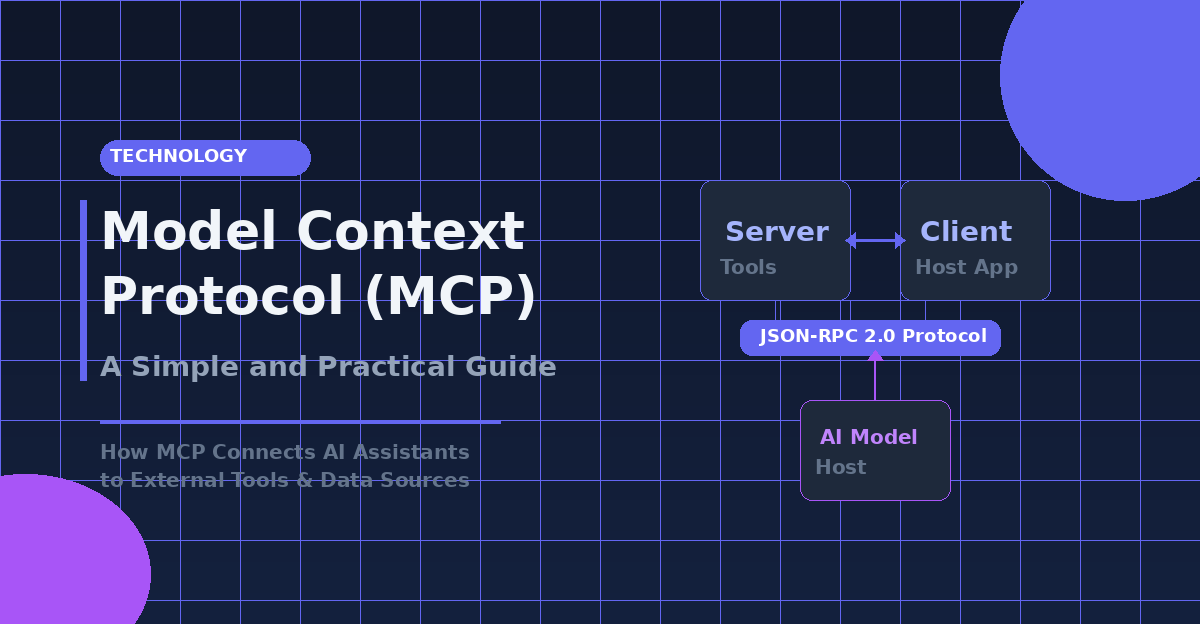
Zero Trust for AI systems requires rethinking identity, data flows, and access control. Learn the five pillars of AI Zero Trust — identity verification, input validation, least privilege, monitoring, and encryption — with practical architecture patterns and implementation roadmap.