The Hmmnm!! platform aims to provide hope and support to students and others through a wide range of resources, including educational materials, experience sharing, emotional assistance, and skill enhancement. It strives to address its reader's internal needs and aspirations, fostering growth in academic, personal, and professional domains through valuable experiences.
Featured Posts
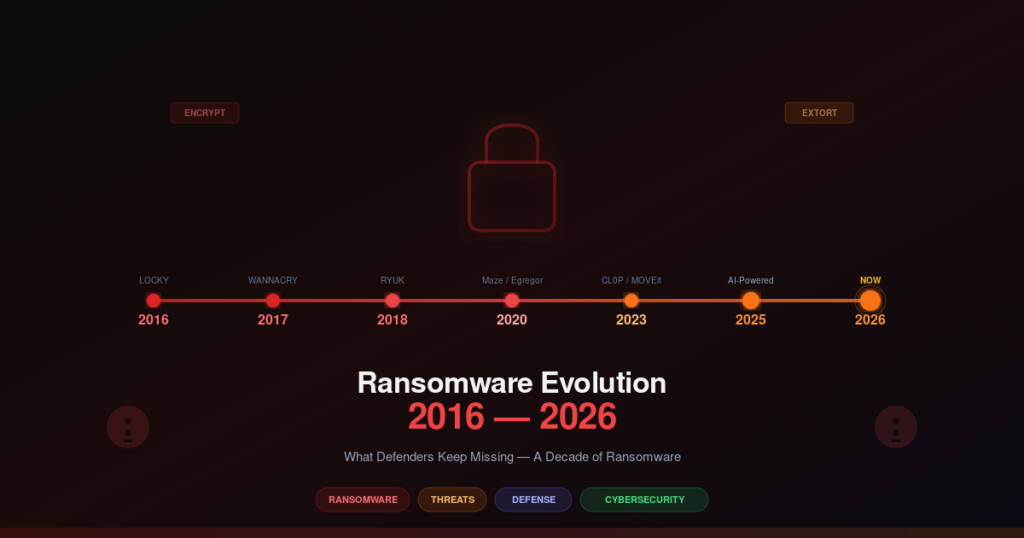
Security
Exploitation techniques, vulnerabilities, and defense strategies
A decade analysis of ransomware evolution from 2016 to 2026, covering RaaS operations, double extortion, initial access brokers, living off...
Read More →A practical guide to software supply chain security covering dependency risks, secrets exposure, CI/CD trust failures, artifact integrity verification, SBOM...
Read More →Deep dive into Server-Side Template Injection (SSTI) vulnerabilities. Learn how template engines can be exploited, detection techniques across Jinja2, Twig,...
Read More →In-depth guide to HTTP request smuggling attacks. Learn how to exploit discrepancies between frontend proxies and backend servers in both...
Read More →10 essential tips for aspiring ethical hackers. Build your cybersecurity career with practical advice on certifications, tool proficiency, lab environments,...
Read More →A practical guide to agentic AI security covering goal hijacking, tool misuse, identity and privilege abuse, memory poisoning, multi-agent trust...
Read More →Prompt injection is the SQL injection of the AI era. In 2026, direct injection, indirect injection, and jailbreaking techniques are...
Read More →How identity became the new perimeter in modern cybersecurity. Explore MFA bypass techniques, OAuth consent phishing, device code attacks, token...
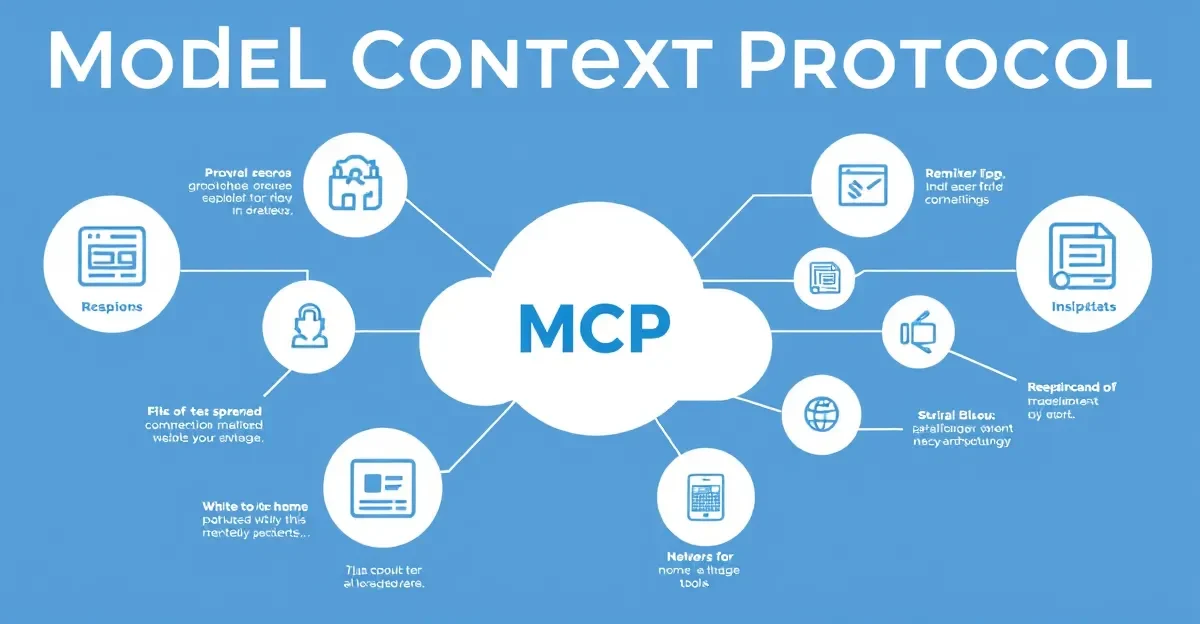
Read More →A comprehensive security assessment of the Model Context Protocol covering threat modeling, attack surface analysis, pentest methodologies, prompt injection test...
Read More →A practical analysis of API security authorization flaws behind modern breaches. Covers BOLA, BFLA, IDOR, mass assignment, shadow APIs, and...
Read More →Complete cross-site scripting (XSS) tutorial covering stored, reflected, and DOM-based XSS with practical exploitation examples and prevention strategies including CSP.
Read More →Learn error-based exploitation techniques used by pentesters to extract sensitive data from vulnerable applications. Covers SQL injection, SSTI, and other...
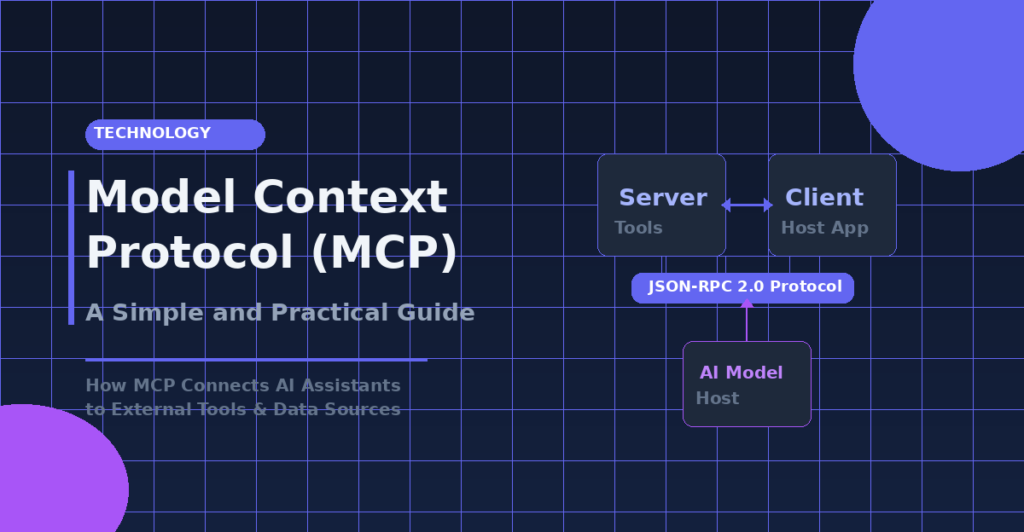
Read More →Technology
MCP, APIs, cloud, and emerging tech deep dives
Google's TurboQuant is a breakthrough AI compression method targeting memory bottlenecks in large language models. This guide explains how TurboQuant...
Read More →Zero Trust for AI systems requires rethinking identity, data flows, and access control. Learn the five pillars of AI Zero...
Read More →Model Context Protocol (MCP) is an open standard enabling AI assistants to communicate with external tools and data sources seamlessly....
Read More →Experience
Real-world stories, Kashmir, and personal journeys
AI is transforming mental health support through chatbots, mood trackers, and diagnostic tools. But can technology replace human empathy? This...
Read More →Kashmir Part 2: The proxy war machinery, media propaganda, Kashmiri Pandit exodus, Pakistan's internal reality, economic recovery efforts, and stories...
Read More →An in-depth exploration of the Kashmir conflict — from the proxy war and Article 370 revocation to the human cost,...
Read More →Travel
Cherrapunji, Rishikesh, and hidden gems in India
Complete travel guide to Rishikesh, the yoga capital of the world. Discover ancient ashrams, adventure activities, spiritual experiences, and practical...
Read More →Cherrapunji travel guide: discover India's pristine paradise with stunning waterfalls, living root bridges, cave systems, and the lush landscapes of...
Read More →Complete travel guide to Kartarpur Sahib Corridor — history of the 72-year wait, how to book online, route from India...
Read More →Food
Recipes, food culture, and culinary adventures
Explore India's love for Chole — from Pindi and Amritsari to Kolkata and South Indian variations. Discover the nutritional power...
Read More →