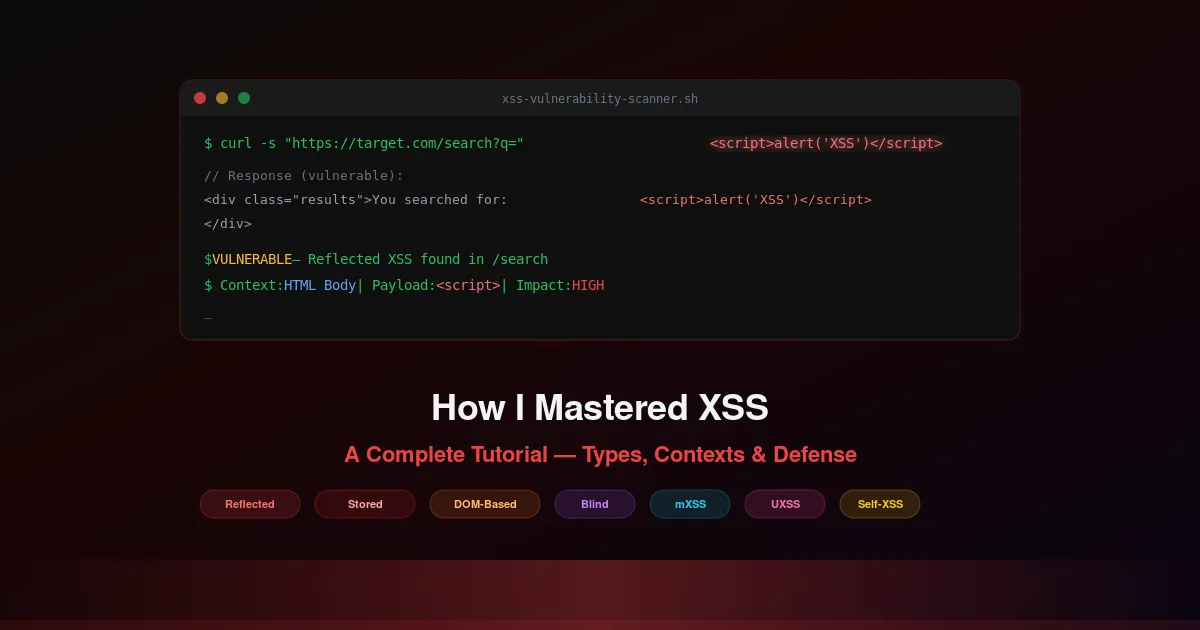
Ensuring Robust Security in Login and Registration Systems
Comprehensive guide to securing login and registration systems. Covers authentication vulnerabilities, brute-force protection, session management, CAPTCHA implementation, and security best practices.